
By Kate Conger
The Republican lawmaker from Georgia cannot tweet for 12 hours, after the White House criticized social media sites for amplifying vaccine lies.
Published: July 18, 2021 at 07:00PM
from NYT Technology https://ift.tt/2VYX39I
via IFTTT


By Kate Conger
The Republican lawmaker from Georgia cannot tweet for 12 hours, after the White House criticized social media sites for amplifying vaccine lies.
Published: July 18, 2021 at 07:00PM
from NYT Technology https://ift.tt/2VYX39I
via IFTTT

By Alyssa Lukpat
From New Hampshire to Scotland, services like Google Maps can direct ill-prepared hikers onto trails that would challenge even the most experienced climbers, mountaineers said.
Published: July 17, 2021 at 07:00PM
from NYT Technology https://ift.tt/3igcQYY
via IFTTT
La herramienta, lanzada por Amnistía Internacional, busca rastros dejados por el software espía Pegasus.
from Digital Trends Español https://ift.tt/3ewN55B
via IFTTT
El exconsultor de inteligencia asegura que los gobiernos tendrían que tomar acción al respecto.
from Digital Trends Español https://ift.tt/3zdGEfN
via IFTTT
DOJ indicts four Chinese individuals for alleged role in attacks targeting intellectual property, trade secrets belonging to defense contractors, maritime companies, aircraft service firms, and others.
from Dark Reading: https://ift.tt/2UXFIgK
via IFTTT
Campbell Conroy & O’Neil reports the attack affected personal data including Social Security numbers, passport numbers, and payment card data for some individuals.
from Dark Reading: https://ift.tt/3kzzgXX
via IFTTT
Estamos seguros de que entre nuestro listado de las mejores marcas de laptops encontrarás la adecuada para ti.
from Digital Trends Español https://ift.tt/2Ofokw8
via IFTTT
Browse the comments on virtually any story about a ransomware attack and you will almost surely encounter the view that the victim organization could have avoided paying their extortionists if only they’d had proper data backups. But the ugly truth is there are many non-obvious reasons why victims end up paying even when they have done nearly everything right from a data backup perspective.

This story isn’t about what organizations do in response to cybercriminals holding their data for hostage, which has become something of a best practice among most of the top ransomware crime groups today. Rather, it’s about why victims still pay for a key needed to decrypt their systems even when they have the means to restore everything from backups on their own.
Experts say the biggest reason ransomware targets and/or their insurance providers still pay when they already have reliable backups is that nobody at the victim organization bothered to test in advance how long this data restoration process might take.
“In a lot of cases, companies do have backups, but they never actually tried to restore their network from backups before, so they have no idea how long it’s going to take,” said Fabian Wosar, chief technology officer at Emsisoft. “Suddenly the victim notices they have a couple of petabytes of data to restore over the Internet, and they realize that even with their fast connections it’s going to take three months to download all these backup files. A lot of IT teams never actually make even a back-of-the-napkin calculation of how long it would take them to restore from a data rate perspective.”
Wosar said the next most-common scenario involves victims that have off-site, encrypted backups of their data but discover that the digital key needed to decrypt their backups was stored on the same local file-sharing network that got encrypted by the ransomware.
The third most-common impediment to victim organizations being able to rely on their backups is that the ransomware purveyors manage to corrupt the backups as well.
“That is still somewhat rare,” Wosar said. “It does happen but it’s more the exception than the rule. Unfortunately, it is still quite common to end up having backups in some form and one of these three reasons prevents them from being useful.”
Bill Siegel, CEO and co-founder of Coveware, a company that negotiates ransomware payments for victims, said most companies that pay either don’t have properly configured backups, or they haven’t tested their resiliency or the ability to recover their backups against the ransomware scenario.
“It can be [that they] have 50 petabytes of backups … but it’s in a … facility 30 miles away.… And then they start [restoring over a copper wire from those remote backups] and it’s going really slow … and someone pulls out a calculator and realizes it’s going to take 69 years [to restore what they need],” Siegel told Kim Zetter, a veteran Wired reporter who recently launched a cybersecurity newsletter on Substack.
“Or there’s lots of software applications that you actually use to do a restore, and some of these applications are in your network [that got] encrypted,” Siegel continued. “So you’re like, ‘Oh great. We have backups, the data is there, but the application to actually do the restoration is encrypted.’ So there’s all these little things that can trip you up, that prevent you from doing a restore when you don’t practice.”
Wosar said all organizations need to both test their backups and develop a plan for prioritizing the restoration of critical systems needed to rebuild their network.
“In a lot of cases, companies don’t even know their various network dependencies, and so they don’t know in which order they should restore systems,” he said. “They don’t know in advance, ‘Hey if we get hit and everything goes down, these are the services and systems that are priorities for basic network that we can build off of.’”
Wosar said it’s essential that organizations drill their breach response plans in periodic tabletop exercises, and that it is in these exercises that companies can start to refine their plans. For example, he said, if the organization has physical access to their remote backup data center, it might make more sense to develop processes for physically shipping the backups to the restoration location.
“Many victims see themselves confronted with having to rebuild their network in a way they didn’t anticipate. And that’s usually not the best time to have to come up with these sorts of plans. That’s why tabletop exercises are incredibly important. We recommend creating an entire playbook so you know what you need to do to recover from a ransomware attack.”
from Krebs on Security https://ift.tt/2UVVyIX
via IFTTT
(adsbygoogle = window.adsbygoogle || []).push({});
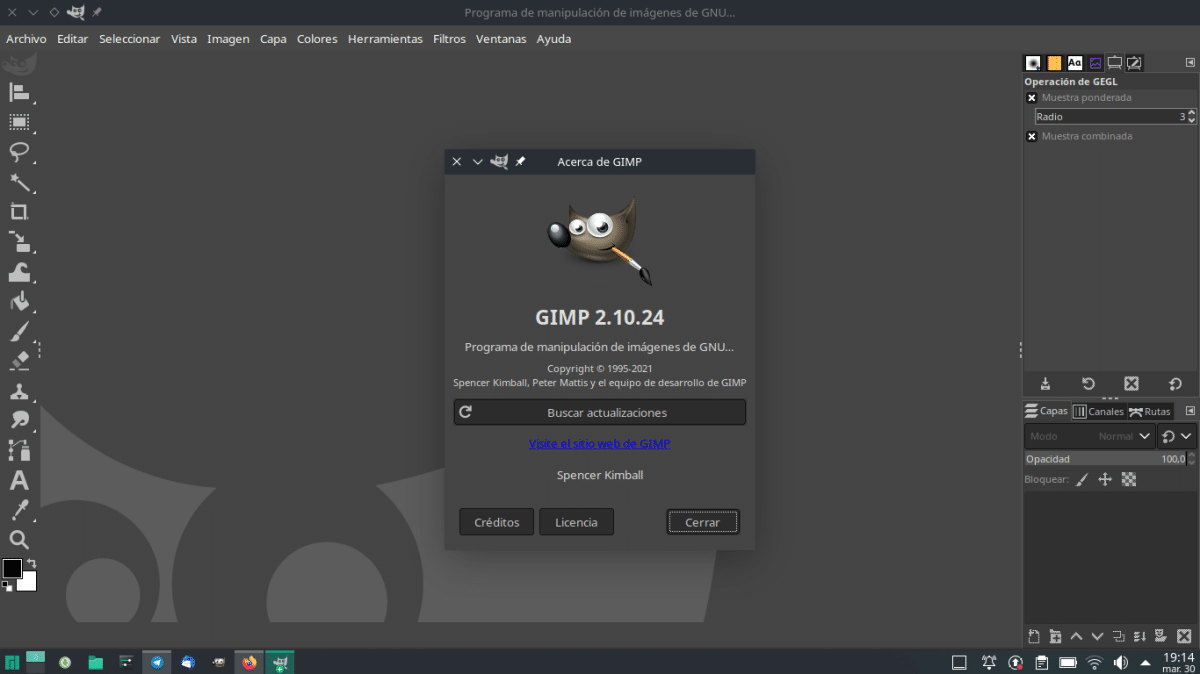
Siempre se ha dicho que las comparaciones son odiosas, y eso es muy cierto cuando hablamos de software. Un programa puede ser peor que otro y ser nuestra elección sólo porque nos sentimos cómodos con él, pero que no conozcamos algunas funciones o que una opción nos guste más que otra no demuestra que sea la mejor. En el diseño gráfico, o más bien en la edición de imágenes, la referencia es el Photoshop de Adobe, y hay alguien que piensa que GIMP podría estar por encima.
Vaya por delante que esto es lo que dice Edward Snowden, y me he enterado de su opinión leyendo un artículo de It’s FOSS. El ex-empleado de la CIA está encantado con Blender, el software de modelado 3D de código abierto, y se llega a sorprender de lo que se puede conseguir con el software open source. Lo ha hecho en Twitter, donde ha añadido un tweet en el que menciona a GIMP asegurando que podría superar a Adobe.
(adsbygoogle = window.adsbygoogle || []).push({});
P.S. @GIMP_Official, I’m really hoping for a major UI overhaul. You guys could be eating Adobe’s lunch.
— Edward Snowden (@Snowden) July 18, 2021
https://platform.twitter.com/widgets.js
Cada vez que uso @Blender, estoy asombrado por lo que puede lograr el software libre y de código abierto. Sinceramente, no sé cómo lo hacen. Es un monumento. PD @GIMP_Official, realmente espero una revisión importante de la interfaz de usuario. Ustedes podrían estar comiendo el almuerzo de Adobe.
En lo personal, sí que creo que el viejo GIMP, con las tres ventanas, necesitaba un cambio urgente, pero ese cambio ya ha tenido lugar. Por otra parte, sé que es capaz de hacer mucho editando imágenes, pero recuerdo que, cuando usé Photoshop, todo me parecía más sencillo, y hacer un GIF animado, con su línea de tiempo, es algo que conseguí hacer en el software de Adobe y, aunque ya no lo necesito, creo que es más difícil en GIMP.
En cualquier caso, de momento GIMP no planea ningún cambio de interfaz. Si se decidiera a hacerlo, ¿creéis que Snowden tiene razón?
from Linux Adictos https://ift.tt/3BichH1
via IFTTT
Tu bocina inteligente Google Home es capaz de hacer mucho por ti… cuando la configuras correctamente.
from Digital Trends Español https://ift.tt/2BosU7s
via IFTTT