The U.S. Department of Justice (DOJ) today seized four-dozen domains that sold “booter” or “stresser” services — businesses that make it easy and cheap for even non-technical users to launch powerful Distributed Denial of Service (DDoS) attacks designed knock targets offline. The DOJ also charged six U.S. men with computer crimes related to their alleged ownership of the popular DDoS-for-hire services.
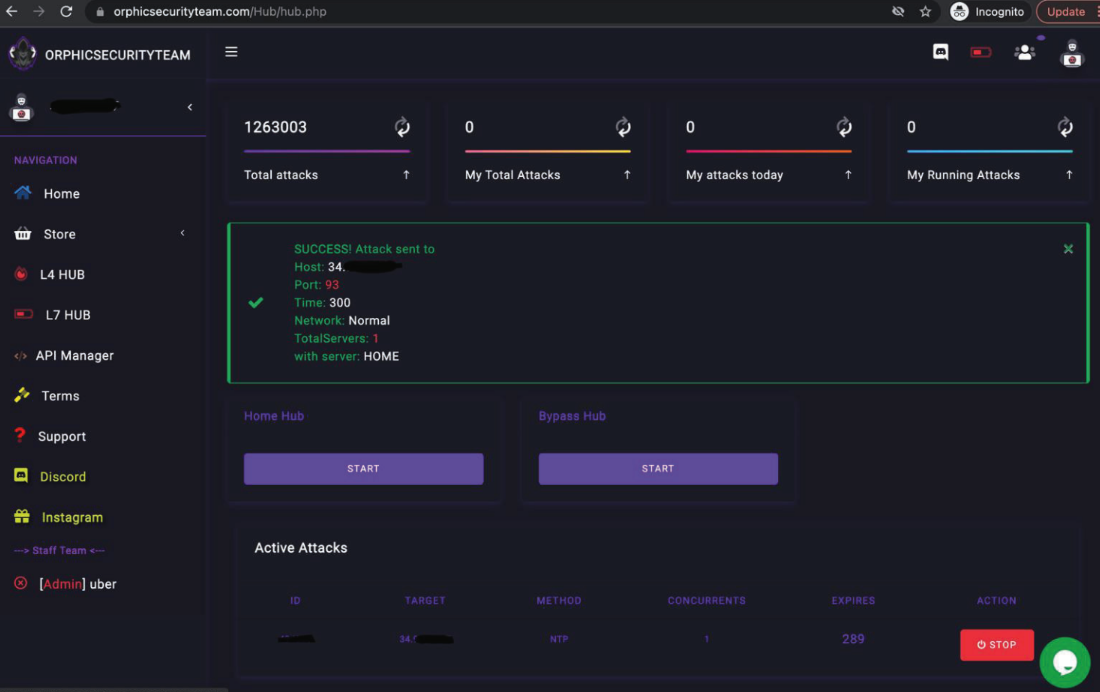
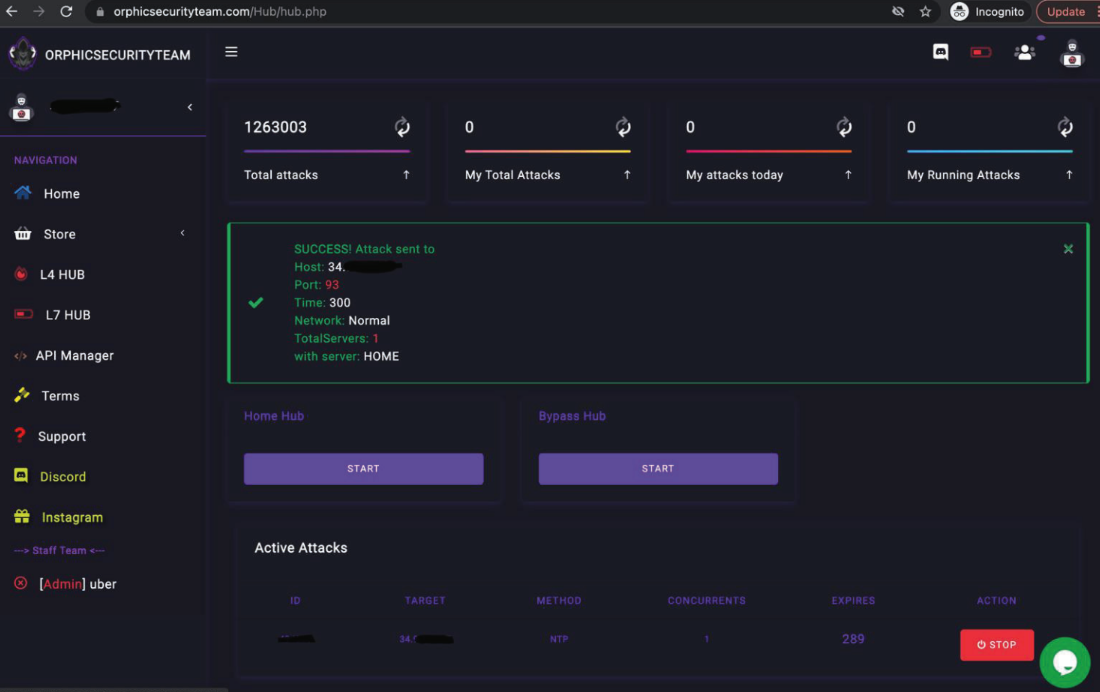
The booter service OrphicSecurityTeam[.]com was one of the 48 DDoS-for-hire domains seized by the Justice Department this week.
The DOJ said the 48 domains it seized helped paying customers launch millions of digital sieges capable of knocking Web sites and even entire network providers offline.
Booter services are advertised through a variety of methods, including Dark Web forums, chat platforms and even youtube.com. They accept payment via PayPal, Google Wallet, and/or cryptocurrencies, and subscriptions can range in price from just a few dollars to several hundred per month. The services are generally priced according to the volume of traffic to be hurled at the target, the duration of each attack, and the number of concurrent attacks allowed.
Prosecutors in Los Angeles say the booter sites supremesecurityteam[.]com and royalstresser[.]com were the brainchild of Jeremiah Sam Evans Miller, a.k.a. “John the Dev,” a 23-year-old from San Antonio, Texas. Miller was charged this week with conspiracy and violations of the Computer Fraud and Abuse Act (CFAA). The complaint against Miller alleges Royalstresser launched nearly 200,000 DDoS attacks between November 2021 and February 2022.
Defendant Angel Manuel Colon Jr., a.k.a Anonghost720 and Anonghost1337, is a 37-year-old from Belleview, Fla. Colon is suspected of running the booter service securityteam[.]io. He was also charged with conspiracy and CFAA violations. The feds say the SecurityTeam stresser service conducted 1.3 million attacks between 2018 and 2022, and attracted some 50,000 registered users.
Charged with conspiracy were Corey Anthony Palmer, 22, of Lauderhill, Fla, for his alleged ownership of booter[.]sx; and Shamar Shattock, 19, of Margate, Fla., for allegedly operating the booter service astrostress[.]com, which had more than 30,000 users and blasted out some 700,000 attacks.
Two other alleged booter site operators were charged in Alaska. John M. Dobbs, 32, of Honolulu, HI is charged with aiding and abetting violations of the CFAA related to the operation of IPStresser[.]com, which he allegedly operated for nearly 13 years until last month. During that time, IPstresser launched approximately 30 million DDoS attacks and garnered more than two million registered users.
Joshua Laing, 32, of Liverpool, NY, also was charged with CFAA infractions tied to his alleged ownership of the booter service TrueSecurityServices[.]io, which prosecutors say had 18,000 users and conducted over 1.2 million attacks between 2018 and 2022.
Purveyors of stressers and booters claim they are not responsible for how customers use their services, and that they aren’t breaking the law because — like most security tools — stresser services can be used for good or bad purposes. For example, all of the above-mentioned booter sites contained wordy “terms of use” agreements that required customers to agree they will only stress-test their own networks — and that they won’t use the service to attack others.
But the DOJ says these disclaimers usually ignore the fact that most booter services are heavily reliant on constantly scanning the Internet to commandeer misconfigured devices that are critical for maximizing the size and impact of DDoS attacks.
“None of these sites ever required the FBI to confirm that it owned, operated, or had any property right to the computer that the FBI attacked during its testing (as would be appropriate if the attacks were for a legitimate or authorized purpose),” reads an affidavit (PDF) filed by Elliott Peterson, a special agent in the FBI’s Anchorage field office.
“Additionally, analysis of data related to the FBI-initiated attacks revealed that the attacks launched by the SUBJECT DOMAINS involved the extensive misuse of third-party services,” Peterson continued. “Specifically, all of the tested services offered ‘amplification’ attacks, where the attack traffic is amplified through unwitting third-party servers in order to increase the overall attack size, and to shift the financial burden of generating and transmitting all of that data away from the booter site administrator(s) and onto third parties.”
According to U.S. federal prosecutors, the use of booter and stresser services to conduct attacks is punishable under both wire fraud laws and the Computer Fraud and Abuse Act (18 U.S.C. § 1030), and may result in arrest and prosecution, the seizure of computers or other electronics, as well as prison sentences and a penalty or fine.
The charges unsealed today stemmed from investigations launched by the FBI’s field offices in Los Angeles and Alaska, which spent months purchasing and testing attack services offered by the booter sites.
A similar investigation initiating from the FBI’s Alaska field office in 2018 culminated in a takedown and arrest operation that targeted 15 DDoS-for-hire sites, as well as three booter store defendants who later pleaded guilty.
The Justice Department says its trying to impress upon people that even buying attacks from DDoS-for-hire services can land Internet users in legal jeopardy.
“Whether a criminal launches an attack independently or pays a skilled contractor to carry one out, the FBI will work with victims and use the considerable tools at our disposal to identify the person or group responsible,” said Donald Alway, the assistant director in charge of the FBI’s Los Angeles field office.
The United Kingdom, which has been battling its fair share of domestic booter bosses, in 2020 started running online ads aimed at young people who search the Web for booter services.
And in Europe, prosecutors have even gone after booter customers.
Here is the full list of booter site domains seized (or in the process of being seized) by the DOJ:
api-sky[.]xyz
astrostress[.]com
blackstresser[.]net
booter[.]sx
booter[.]vip
bootyou[.]net
brrsecurity[.]org
buuter[.]cc
cyberstress[.]us
defconpro[.]net
dragonstresser[.]com
dreams-stresser[.]io
exotic-booter[.]com
freestresser[.]so
instant-stresser[.]com
ipstress[.]org
ipstress[.]vip
ipstresser[.]com
ipstresser[.]us
ipstresser[.]wtf
ipstresser[.]xyz
kraysec[.]com
mcstorm[.]io
nightmarestresser[.]com
orphicsecurityteam[.]com
ovhstresser[.]com
quantum-stresser[.]net
redstresser[.]cc
royalstresser[.]com
securityteam[.]io
shock-stresser[.]com
silentstress[.]net
stresser[.]app
stresser[.]best
stresser[.]gg
stresser[.]is
stresser[.]net/stresser[.]org
stresser[.]one
stresser[.]shop
stresser[.]so
stresser[.]top
stresserai[.]com
sunstresser[.]com
supremesecurityteam[.]com
truesecurityservices[.]io
vdos-s[.]co
zerostresser[.]com
from Krebs on Security https://ift.tt/iT4Z2Ec
via IFTTT