Si se explotan, estas fallas pueden permitir a los atacantes obtener acceso no autorizado a información confidencial o, en general, causar problemas
(adsbygoogle = window.adsbygoogle || []).push({});
Hace poco dieron a conocer mediante una publicación de blog los resultados de un experimento, en el cual demuestran como se puede tomar el control de los paquetes en el repositorio AUR.
Para quienes desconocen de AUR (Arch User Repository), deben saber que este es un repositorio de software para Arch Linux. Se diferencia de los repositorios oficiales de Arch Linux, ya que en este sus paquetes son proporcionados por sus usuarios y Arch Linux no los admite oficialmente.
(adsbygoogle = window.adsbygoogle || []).push({});
AUR es utilizado por desarrolladores externos para distribuir sus paquetes sin estar incluidos en los repositorios principales de la distribución Arch Linux.
En este, se realizó una investigación debido a la falta de soporte, que es más una característica que un error, ya que permite que AUR contenga paquetes que son difíciles de soportar (por ejemplo, debido a problemas de licencia) o que solo son utilizados por un puñado de usuarios.
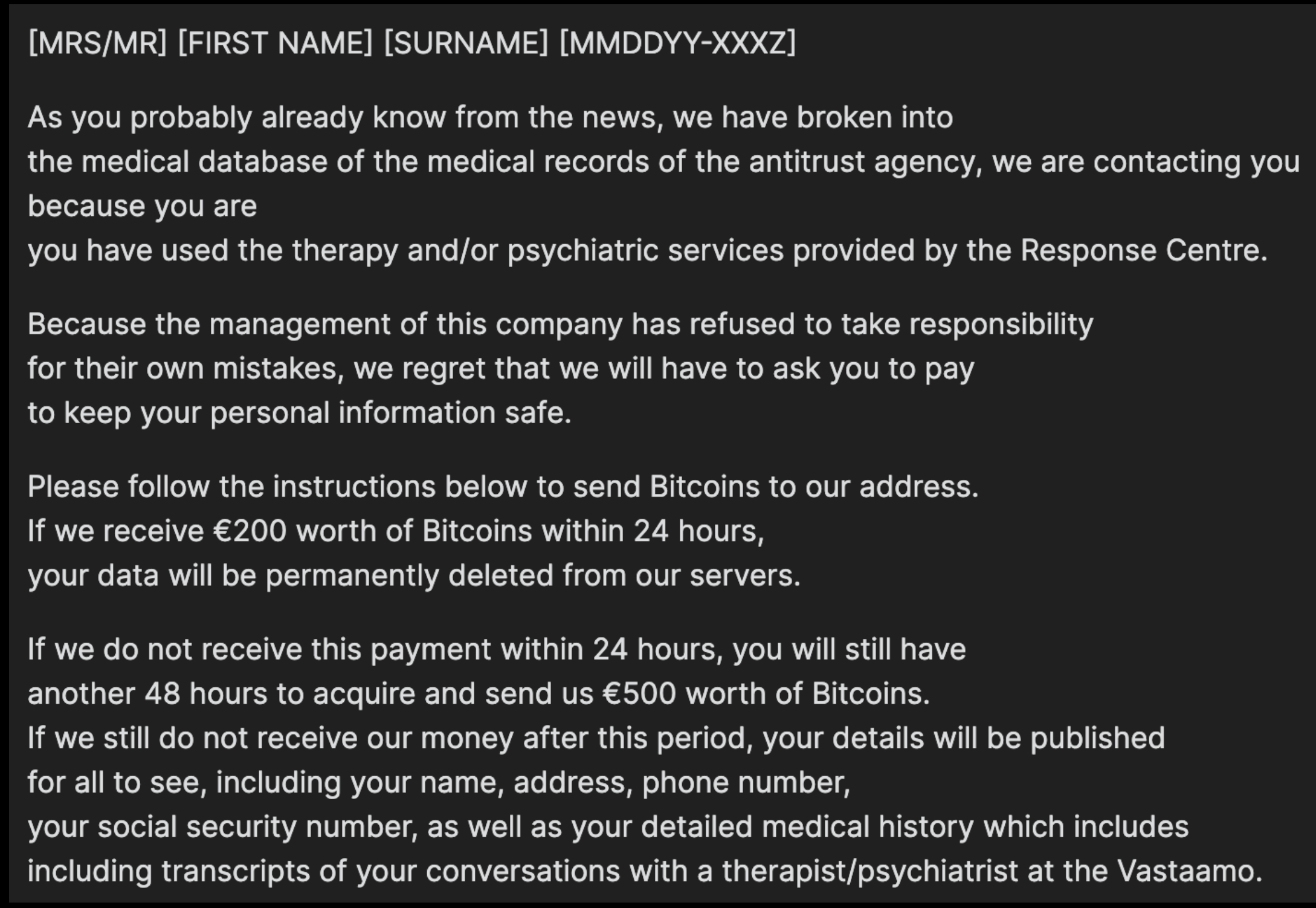
Sin embargo, la falta de soporte también significa menos control de calidad, lo que permite a los malos actores introducir paquetes maliciosos. Para advertir a los usuarios de este riesgo, AUR tiene un gran descargo de responsabilidad en la página principal (una leyenda que muchos ignoran o simplemente desconocen):
ESCARGO DE RESPONSABILIDAD: Los paquetes AUR son contenido producido por el usuario. Cualquier uso de los archivos proporcionados es bajo su propio riesgo.
Sobre el experimento realizado, los investigadores prepararon un script que comprueba la caducidad del registro de los dominios que aparecen en los archivos PKGBUILD y SRCINFO. La ejecución de este script identificó 14 dominios caducados utilizados en 20 paquetes de carga de archivos.
(adsbygoogle = window.adsbygoogle || []).push({});
Con ello, pudieron identificar que hay varias formas de introducir un paquete malicioso (o cambios maliciosos en un paquete legítimo) en AUR. Por ejemplo, convirtiéndose en el mantenedor de paquetes huérfanos (es decir, paquetes que ya no son compatibles con sus mantenedores anteriores) o escribiendo nombres de paquetes populares.
Otra opción es encontrar paquetes que utilicen URL con dominios caducados durante su proceso de creación, registrar el dominio y alojar archivos maliciosos. ¿Cuántos de los paquetes son vulnerables a tal ataque? ¡Vamos a averiguar!
Se menciona que el proceso no es tan simple como se pudiera tener en cuenta, ya no basta simplemente con registrar un dominio, ya que esto no es suficiente para falsificar el paquete, pues el contenido descargado se compara con la suma de verificación ya cargada en AUR. Sin embargo, los mantenedores de alrededor del 35% de los paquetes en AUR parecen usar el parámetro «SKIP» en el archivo PKGBUILD para omitir la verificación de la suma de control (por ejemplo, especifique sha256sums=(‘SKIP’)). De los 20 paquetes con dominios vencidos, en 4 se utilizó el parámetro SKIP.
Para demostrar la posibilidad de cometer un ataque, los investigadores compraron el dominio de uno de los paquetes que no verifican las sumas de verificación y colocaron un archivo con el código y un script de instalación modificado.
Desafortunadamente, no existe una forma estandarizada de verificar si un dominio está disponible. Las respuestas de WHOIS de los TLD más populares contienen algo como «No coincide con el dominio» para los dominios disponibles, pero esto no es cierto para todos los TLD. Un buen primer paso es filtrar cualquier dominio que tenga un Aconjunto de registros DNS, ya que esos dominios (lo más probable) todavía estarán en uso. Para realizar rápidamente muchas solicitudes de DNS, usamos blechschmidt/massdns . Esta es una gran herramienta que nos permite resolver miles de dominios en segundos
En lugar del contenido real, se ha agregado al script una advertencia sobre la ejecución de código de terceros. Un intento de instalar el paquete condujo a la descarga de archivos falsificados y, dado que no se verificó la suma de verificación, a la instalación y ejecución exitosas del código agregado por los experimentadores.
(adsbygoogle = window.adsbygoogle || []).push({});
Finalmente se menciona que el secuestro de paquetes AUR no es un concepto nuevo, ya que el secuestro de paquetes AUR siempre ha sido posible (de múltiples maneras) y es un riesgo conocido.
Si estás interesado en poder conocer más al respecto, puedes consultar los detalles en el siguiente enlace.
from Linux Adictos https://ift.tt/29MItDJ
via IFTTT