Recent studies show that before automation can reduce the burden on understaffed cybersecurity teams, they need to bring in enough automation skills to run the tools.
from Dark Reading: https://ubm.io/2VNWESt
via IFTTT

Recent studies show that before automation can reduce the burden on understaffed cybersecurity teams, they need to bring in enough automation skills to run the tools.
from Dark Reading: https://ubm.io/2VNWESt
via IFTTT

Troll Genius Builds A PC Case Out Of Freakin’ Lasagna
This man deserves a spot in the pantheon of great technologists.
April 18, 2019 at 02:09PM
via Digg http://bit.ly/2vchdME
Cuando decimos que Android es un sistema operativo “libre”, no solo nos referimos –aunque también– a la posibilidad de elegir entre cientos de modelos de dispositivos de decenas de marcas diferentes. Más allá de eso, la plataforma de Google también nos ofrece la posibilidad de modificar la experiencia con nuestros dispositivos y hacerla totalmente única, gracias a las diversas opciones de personalización disponibles en Android. De hecho, las posibilidades a
Entra en Andro4all para leer el artículo completo
Puedes unirte a nosotros en Twitter, Facebook o en Google+
¡Suscríbete a nuestro canal de YouTube!
Publicado recientemente en Andro4all
from Andro4all http://bit.ly/2VgVVwh
via IFTTT
Improving processes won’t happen overnight, but it’s not complicated either.
from Dark Reading: https://ubm.io/2Djuyaw
via IFTTT

La famosa empresa de desarrollo de videojuegos Ubisoft de origen frances anunció el dia de ayer que participará en la gran ola de apoyo que surgió luego del incendio que devastó la Catedral de Notre-Dame en París.
En forma de un tributo que permitirá a todos los jugadores obtenga una copia gratuita de Assassin’s Creed Unity para PC durante una semana (tienen hasta el 25 de abril) y permita a los jugadores caminar alrededor de una catedral de Notre-Dame durante la Revolución Francesa.
(adsbygoogle = window.adsbygoogle || []).push({});
El incendio que devastó el lunes pasado al monumento de nueve siglos provocó una ola de entusiasmo en Francia y en el extranjero, empujando a la gente a donar para su reconstrucción.
El regalo de Assassin’s Creed Unity por parte de Ubisoft no se eligió al azar, si no que, el juego se lleva a cabo en París en la epoca de 1789 y en donde los jugadores de este gran titulo forman parte de una sociedad secreta de asesinos que vagan por la ciudad en busca de las víctimas de un grupo rival.
Para quienes desconozcan de este titulo y se pregunte el ¿por que?, deben saber que Assassin’s Creed Unity incluye una versión digital en 3D de la Catedral de Notre-Dame, basada en planos reales así como basada en los documentos históricos e imágenes de estatuas y piedras antiguas. La reproducción requirió 5,000 horas de trabajo y requirió la reconstitución de 140 vitrales.
(adsbygoogle = window.adsbygoogle || []).push({});
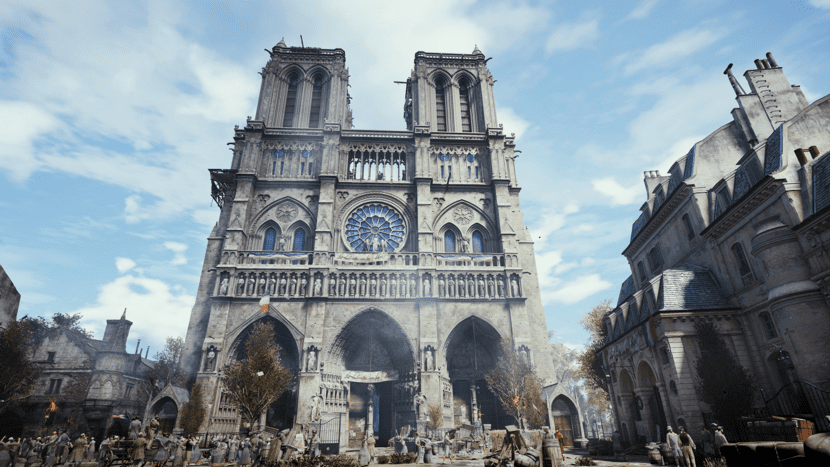
Los jugadores pueden escalar los arcos y las gárgolas de la catedral y admirar una reconstrucción del panorama del siglo XVIII en París.
Sin embargo, hay un pequeño detalle que no encaja y es que en la catedral ya tiene su aguja, pero se añadió a mediados del siglo XIX.
Ubisoft se solidariza con la parisina y todas las personas en todo el mundo se mueve por este trágico suceso. Notre-Dame es una parte integral de la identidad de París y Francia, una ciudad a la que estamos profundamente conectados. Ver a la catedral en llamas nos afectó profundamente a todos.
Al crear el juego Assassin’s Creed Unity, Ubisoft tuvo la oportunidad de establecer vínculos aún más estrechos con París, así como con todos sus monumentos históricos.
Ubisoft ha concentrado gran parte de su tiempo y esfuerzo en la reconstrucción de Notre-Dame, para acercarse al original
A la luz de los eventos del lunes, Ubisoft quiere dejar que la majestuosidad y la belleza de la catedral se descubran de la mejor manera posible.
A partir de hoy y durante toda una semana, Ubisoft ofrece la versión para PC de Assassin’s Creed Unity para todos aquellos que la deseen.
Para quienes estén interesados en poder obtener su copia gratuita de Assassin’s Creed Unity, deben saber que el juego ya está disponible (desde el dia de ayer) para descargar en desde Uplay (la plataforma de juegos de Ubisoft).
Para poder reclamar su copia deben dirigirse al siguiente enlace o directamente en la tienda de Ubisoft
Además de esta generoso regalo por parte de Ubisoft, también se compromete con € 500,000 para ayudar a restaurar y reconstruir Notre-Dame de Paris.
Ubisoft también alienta a todos aquellos que deseen contribuir a este esfuerzo colectivo.
“Se ha considerado a Assassin’s Creed Unity como un último tributo a la ciudad de París, y Ubisoft espera que Notre-Dame encuentre su brillo brillante lo más rápido posible”.
Ahora la parte final para quienes usamos Linux. Para ejecutar Assassin’s Creed Unity en nuestra distribución favorita podremos hacer uso de algunas herramientas.
Entre las cuales podremos destacar a Lutris, Wine, PlayOnLinux y Crossover.
De ellos yo de manera personal recomiendo a Lutris (totalmente gratuito) o para quienes tengan una licencia de Crossover o utilicen Deepin OS hagan uso de este.
Ya que estas dos herramientas automatizan el proceso de instalación y de la configuración de las bibliotecas de Wine (dll) necesarias.
El artículo Assassin’s Creed Unity gratis por una semana en apoyo a Notre-Dame ha sido originalmente publicado en Linux Adictos.
from Linux Adictos http://bit.ly/2Irl3dv
via IFTTT

By ERIN GRIFFITH
Public market investors warmed to Pinterest during its pitches ahead of its market debut.
Published: April 17, 2019 at 07:00PM
from NYT Technology https://nyti.ms/2VNuqY1
via IFTTT

Facebook Now Says Its Password Leak Affected ‘millions’ Of Instagram Users
Facebook has confirmed its password-related security incident last month now affects “millions” of Instagram users, not “tens of thousands” as first thought.
April 18, 2019 at 01:21PM
via Digg https://tcrn.ch/2IIXrAn
The crooks responsible for launching phishing campaigns that netted dozens of employees and more than 100 computer systems last month at Wipro, India’s third-largest IT outsourcing firm, also appear to have targeted a number of other competing providers, including Infosys and Cognizant, new evidence suggests. The clues so far suggest the work of a fairly experienced crime group that is focused on perpetrating gift card fraud.
On Monday, KrebsOnSecurity broke the news that multiple sources were reporting a cybersecurity breach at Wipro, a major trusted vendor of IT outsourcing for U.S. companies. The story cited reports from multiple anonymous sources who said Wipro’s trusted networks and systems were being used to launch cyberattacks against the company’s customers.
In a follow-up story Wednesday on the tone-deaf nature of Wipro’s public response to this incident, KrebsOnSecurity published a list of “indicators of compromise” or IOCs, telltale clues about tactics, tools and procedures used by the bad guys that might signify an attempted or successful intrusion.
If one examines the subdomains tied to just one of the malicious domains mentioned in the IoCs list (internal-message[.]app), one very interesting Internet address is connected to all of them — 185.159.83[.]24. This address is owned by King Servers, a well-known bulletproof hosting company based in Russia.
According to records maintained by Farsight Security, that address is home to a number of other likely phishing domains:
securemail.pcm.com.internal-message[.]app
secure.wipro.com.internal-message[.]app
securemail.wipro.com.internal-message[.]app
secure.elavon.com.internal-message[.]app
securemail.slalom.com.internal-message[.]app
securemail.avanade.com.internal-message[.]app
securemail.infosys.com.internal-message[.]app
securemail.searshc.com.internal-message[.]app
securemail.capgemini.com.internal-message[.]app
securemail.cognizant.com.internal-message[.]app
secure.rackspace.com.internal-message[.]app
securemail.virginpulse.com.internal-message[.]app
secure.expediagroup.com.internal-message[.]app
securemail.greendotcorp.com.internal-message[.]app
secure.bridge2solutions.com.internal-message[.]app
ns1.internal-message[.]app
ns2.internal-message[.]app
mail.internal-message[.]app
ns3.microsoftonline-secure-login[.]com
ns4.microsoftonline-secure-login[.]com
tashabsolutions[.]xyz
http://www.tashabsolutions[.]xyz
The subdomains listed above suggest the attackers may also have targeted American retailer Sears; Green Dot, the world’s largest prepaid card vendor; payment processing firm Elavon; hosting firm Rackspace; business consulting firm Avanade; IT provider PCM; and French consulting firm Capgemini, among others. KrebsOnSecurity has reached out to all of these companies for comment, and will update this story in the event any of them respond with relevant information.
It appears the attackers in this case are targeting companies that in one form or another have access to either a ton of third-party company resources, and/or companies that can be abused to conduct gift card fraud.
Wednesday’s follow-up on the Wipro breach quoted an anonymous source close to the investigation saying the criminals responsible for breaching Wipro appear to be after anything they can turn into cash fairly quickly. That source, who works for a large U.S. retailer, said the crooks who broke into Wipro used their access to perpetrate gift card fraud at the retailer’s stores.
Another source said the investigation into the Wipro breach by a third party company has determined so far the intruders compromised more than 100 Wipro systems and installed on each of them ScreenConnect, a legitimate remote access tool. Investigators believe the intruders were using the ScreenConnect software on the hacked Wipro systems to connect remotely to Wipro client systems, which were then used to leverage further access into Wipro customer networks.
This is remarkably similar to activity that was directed in 2016 and 2017 against Cognizant, one of Wipro’s competitors and likely the target of the same attackers. In May 2018, Maritz Holdings Inc., a Missouri-based firm that handles customer loyalty and gift card programs for third-parties, sued Cognizant (PDF), saying a forensic investigation determined that hackers had broken into Cognizant’s systems and used them to pivot attacks into Maritz’s loyalty program and siphon more than $11 million in fraudulent eGift cards.
That investigation determined the attackers also used ScreenConnect to access computers belonging to Maritz employees. “This was the same tool that was used to effectuate the cyber-attack in Spring 2016. Intersec [the forensic investigator] also determined that the attackers had run searches on the Maritz system for certain words and phrases connected to the Spring 2016 attack.”
According to the lawsuit by Maritz Holdings, investigators also determined that the “attackers were accessing the Maritz system using accounts registered to Cognizant. For example, in April 2017, someone using a Cognizant account utilized the “fiddler” hacking program to circumvent cyber protections that Maritz had installed several weeks earlier.”
Maritz said its forensic investigator found the attackers had run searches on the Maritz system for certain words and phrases connected to the Spring 2016 eGift card cashout. Likewise, my retailer source in the Wipro attack told KrebsOnSecurity that the attackers who defrauded them also searched their systems for specific phrases related to gift cards, and for clues about security systems the retailer was using.
It’s unclear if the work of these criminal hackers is tied to a specific, known threat group. But it seems likely that the crooks who hit Wipro have been targeting similar companies for some time now, and with a fair degree of success in translating their access to cash given the statements by my sources in the Wipro breach and this lawsuit against Cognizant.
What’s remarkable is how many antivirus companies still aren’t flagging as malicious many of the Internet addresses and domains listed in the IoCs, as evidenced by a search at virustotal.com.
from Krebs on Security http://bit.ly/2GuECzy
via IFTTT

Long Lost ‘Zork’ Source Code Uploaded to GitHub, But Few People Understand It
With access to the source code, a group of dedicated fans is now tinkering with the Zork Implementation Language (ZIL).
April 18, 2019 at 12:16PM
via Digg http://bit.ly/2GwFDao
Hisense es una firma de la que no se ha hablado mucho durante los últimos años en el ámbito de la telefonía móvil. A pesar de ello, volvió a estar en primera plana de la actualidad durante el pasado CES de Las Vegas, donde presentó el Hisense U30, su primer terminal con agujero en la pantalla. La firma de origen chino también ha renovado su gama media durante estos primeros
Entra en Andro4all para leer el artículo completo
Puedes unirte a nosotros en Twitter, Facebook o en Google+
¡Suscríbete a nuestro canal de YouTube!
Publicado recientemente en Andro4all
from Andro4all http://bit.ly/2VWgcEg
via IFTTT