On Feb. 21, 2019, KrebsOnSecurity contacted Italian restaurant chain Buca di Beppo after discovering strong evidence that two million credit and debit card numbers belonging to the company’s customers were being sold in the cybercrime underground. Today, Buca’s parent firm announced it had remediated a 10-month breach of its payment systems at dozens of restaurants, including some locations of its other brands such as Earl of Sandwich and Planet Hollywood.
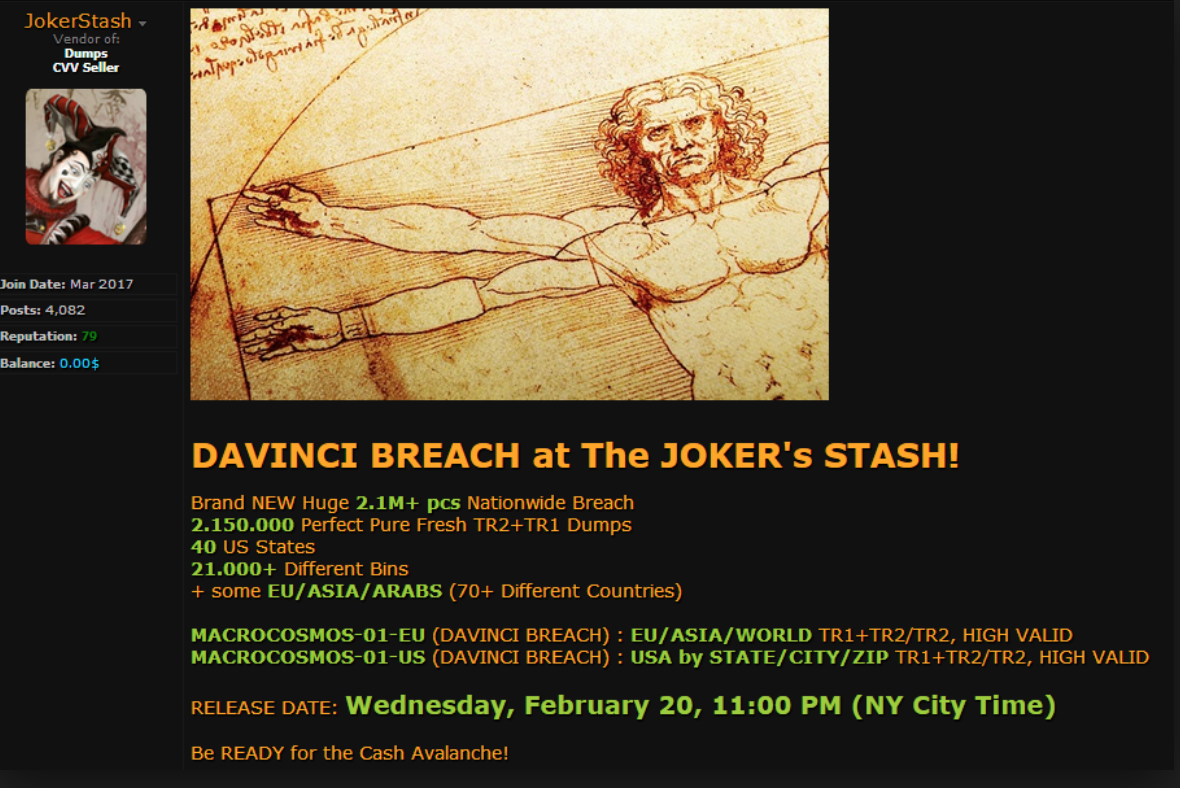
Some 2.1 million+ credit and debit card accounts stolen from dozens of Earl Enterprises restaurant locations went up for sale on a popular carding forum on Feb. 20, 2019.
In a statement posted to its Web site today, Orlando, Fla. based hospitality firm Earl Enterprises said a data breach involving malware installed on its point-of-sale systems allowed cyber thieves to steal card details from customers between May 23, 2018 and March 18, 2019.
Earl Enterprises did not respond to requests for specifics about how many customers total may have been impacted by the 10-month breach. The company’s statement directs concerned customers to an online tool that allows one to look up breached locations by city and state.
According to an analysis of that page, it appears the breach impacts virtually all 67 Buca di Beppo locations in the United States; a handful out of the total 31 Earl of Sandwich locations; and Planet Hollywood locations in Las Vegas, New York City and Orlando. Also impacted were Tequila Taqueria in Las Vegas; Chicken Guy! in Disney Springs, Fla.; and Mixology in Los Angeles.
KrebsOnsecurity contacted the executive team at Buca di Beppo in late February after determining most of this restaurant’s locations were likely involved a data breach that first surfaced on Joker’s Stash, an underground shop that sells huge new batches of freshly-stolen credit and debit cards on a regular basis.
Joker’s Stash typically organizes different batches of stolen cards around a codename tied to a specific merchant breach. This naming convention allows criminals who purchased cards from a specific batch and found success using those cards fraudulently to buy from the same batch again when future cards stolen from the same breached merchant are posted for sale.
While a given batch’s nickname usually has little relation to the breached merchant, Joker’s Stash does offer a number of search options for customers that can sometimes be used to trace a large batch of stolen cards back to a specific merchant.
This is especially true if the victim merchant has a number of store locations in multiple smaller U.S. towns. That’s because while Joker’s Stash makes its stolen cards searchable via a variety of qualities — the card-issuing bank or expiration date, for example — perhaps the most useful in this case is the city or ZIP code tied to each card.
As with a number of other carding sites, Joker’s Stash indexes cards by the city and/or ZIP code of the store from which the card was stolen (not the ZIP code of the affected cardholders).
On Feb. 20, Joker’s Stash moved a new batch of some 2.15 million stolen cards that it dubbed the “Davinci Breach.” An analysis of the cities and towns listed among the Davinci cards for sale included a number of hacked store locations that were not in major cities, such as Burnsville, Minn., Levonia, Mich., Midvale, Utah, Norwood, Ohio, and Wheeling, Ill.
Earl Enterprises said in its statement the malicious software installed at affected stores captured payment card data, which could have included credit and debit card numbers, expiration dates and, in some cases, cardholder names. The company says online orders were not affected.
Malicious hackers typically steal card data from organizations by hacking into point-of-sale systems remotely and seeding those systems with malicious software that can copy account data stored on a card’s magnetic stripe. Thieves can use that data to clone the cards and then use the counterfeits to buy high-priced merchandise from electronics stores and big box retailers.
Cardholders are not responsible for fraudulent charges, but your bank isn’t always going to detect card fraud. That’s why it’s important to regularly review your monthly statements and quickly report any unauthorized charges.
from Krebs on Security https://ift.tt/2WqIPt8
via IFTTT