In the early days of the Internet, there was a period when Internet Protocol version 4 (IPv4) addresses (e.g. 4.4.4.4) were given out like cotton candy to anyone who asked. But these days companies are queuing up to obtain new IP space from the various regional registries that periodically dole out the prized digits. With the value of a single IP hovering between $15-$25, those registries are now fighting a wave of shady brokers who specialize in securing new IP address blocks under false pretenses and then reselling to spammers. Here’s the story of one broker who fought back in the courts, and lost spectacularly.

On May 14, South Carolina U.S. Attorney Sherri Lydon filed criminal wire fraud charges against Amir Golestan, alleging he and his Charleston, S.C. based company Micfo LLC orchestrated an elaborate network of phony companies and aliases to secure more than 735,000 IPs from the American Registry for Internet Numbers (ARIN), a nonprofit which oversees IP addresses assigned to entities in the U.S., Canada, and parts of the Caribbean.
Interestingly, Micfo itself set this process in motion late last year when it sued ARIN. In December 2018, Micfo’s attorneys asked a federal court in Virginia to issue a temporary restraining order against ARIN, which had already told the company about its discovery of the phony front companies and was threatening to revoke some 735,000 IP addresses. That is, unless Micfo agreed to provide more information about its operations and customers.
At the time, many of the IP address blocks assigned to Micfo had been freshly resold to spammers. Micfo ultimately declined to provide ARIN the requested information, and as a result the court denied Micfo’s request (the transcript of that hearing is instructive and amusing).
But by virtue of the contract Micfo signed with ARIN, any further dispute had to be settled via arbitration. On May 13, that arbitration panel ordered Micfo to pay $350,000 for ARIN’s legal fees and to cough up any of those 735,000 IPs the company hadn’t already sold.
According to the criminal indictment in South Carolina, in 2017 and 2018 Golestan sold IP addresses using a third party broker:
“Golestan sold 65,536 IPv4 addresses for $13 each, for a total of $851,896,” the indictment alleges. “Golestan also organized a second transaction for another 65,536 IP addresses, for another approximately $1 million. During this same time period, Golestan had a contract to sell 327,680 IP addresses at $19 per address, for a total of $6.22 million” [this last transaction would be blocked.]
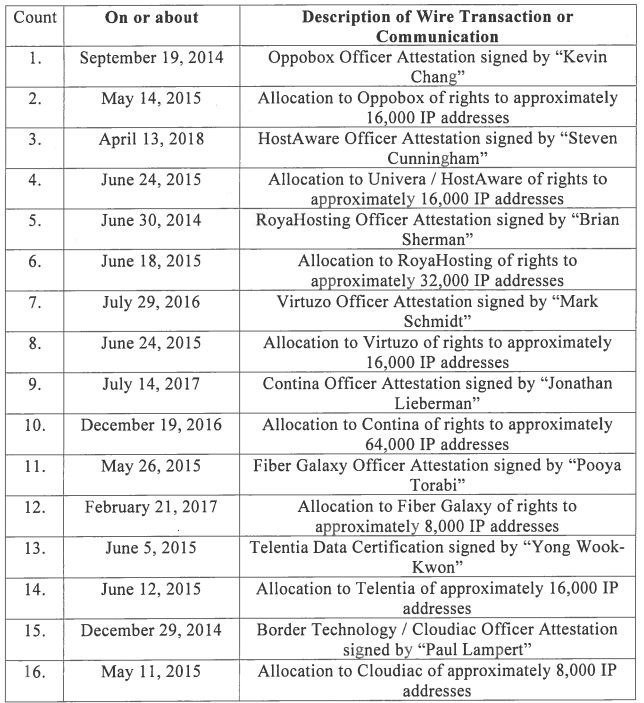
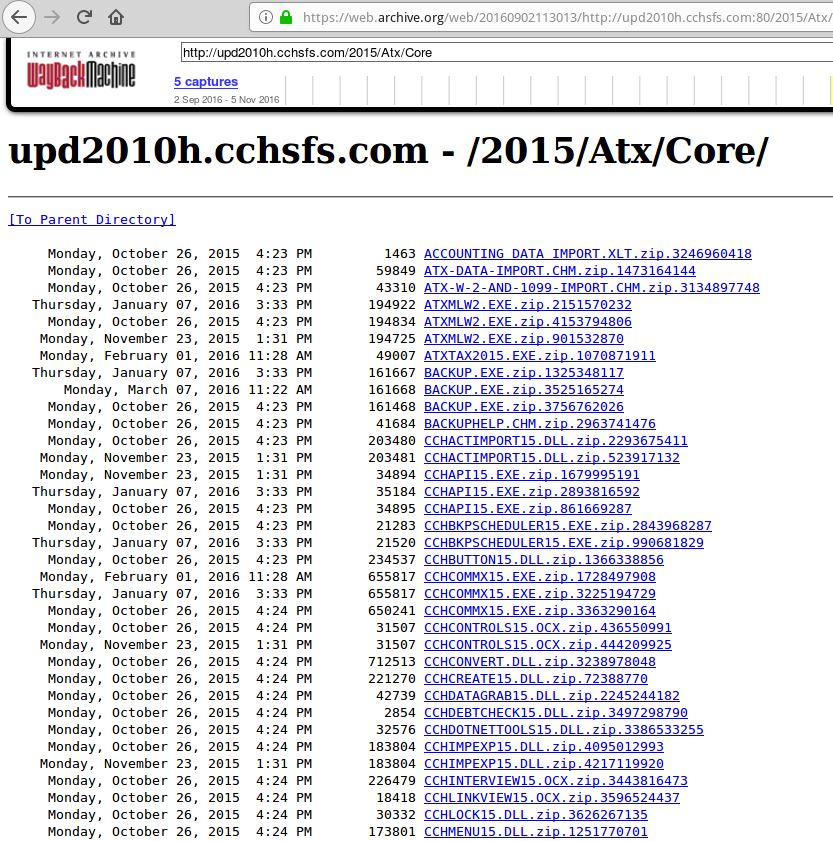
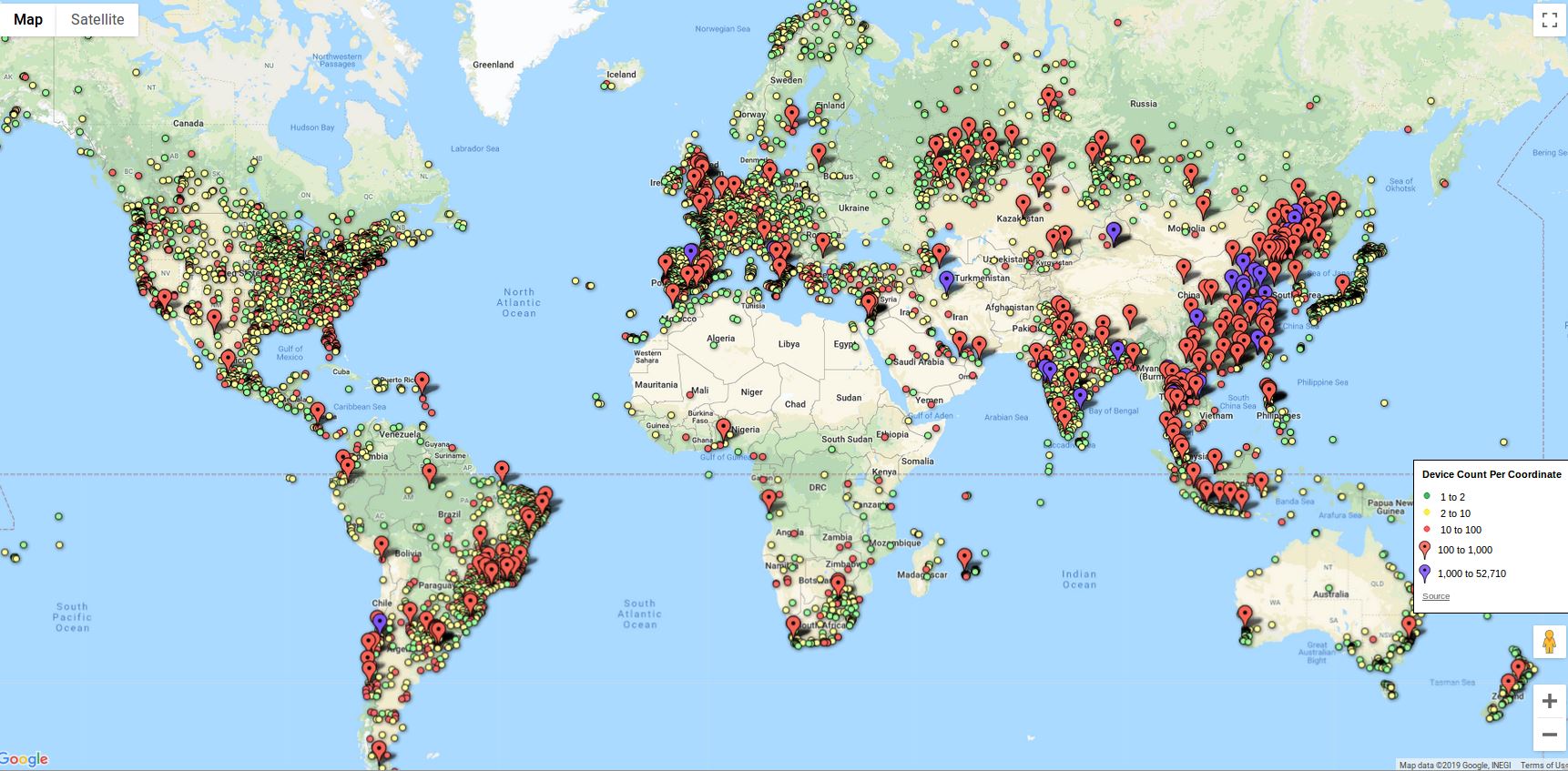
The various front companies alleged to have been run by Micfo and Amir Golestan.
Mr. Golestan could not be immediately reached for comment. Golestan’s attorney in Micfo’s lawsuit against ARIN declined to comment on either the criminal charges or the arbitration outcome. Calls to nearly a dozen of the front companies named in the dispute mostly just rang and rang with no answer, or went to voicemail boxes that were full.
Stephen Ryan is a Washington, D.C.-based attorney who represented ARIN in the dispute filed by Micfo. Ryan said this was the first time ARIN’s decision to revoke IP address space resulted in a court battle — let alone arbitration.
“We have revoked addresses for fraud before, but that hasn’t previously resulted in litigation,” Ryan said. “The interesting thing here is that they litigated this for five months.”
According to a press release by ARIN, “Micfo obtained and utilized 11 shelf companies across the United States, and intentionally created false aliases purporting to be officers of those companies, to induce ARIN into issuing the fraudulently sought IPv4 resources and approving related transfers and reassignments of these addresses. The defrauding party was monetizing the assets obtained in the transfer market, and obtained resources under ARIN’s waiting list process.”
“This was an elaborate operation,” said Ryan, a former federal prosecutor. “All eleven of these front companies for Micfo are still up on the Web, where you see all these wonderful people who allegedly work there. And meanwhile we were receiving notarized affidavits in the names of people that were false. It made it much more interesting to do this case because it created 11 states where they’d violated the law.”
The criminal complaint against Golestan and Micfo (PDF) includes 20 counts of wire fraud associated with the phony companies allegedly set up by Micfo.
John Levine, author of The Internet for Dummies and a member of the security and stability advisory committee at ICANN, said ARIN does not exactly have a strong reputation for going after the myriad IP address scammers allegedly operating in a similar fashion as Micfo.
“It is definitely the case that for a long time ARIN has not been very aggressive about checking the validity of IP address applications and transfers, and now it seems they are somewhat better than they used to be,” Levine said. “A lot of people have been frustrated that ARIN doesn’t act more like a regulator in this space. Given how increasingly valuable IPv4 space is, ARIN has to be more vigilant because the incentive for crooks to do this kind of thing is very high.”
Asked if ARIN would have the stomach and budget to continue the fight if other IP address scammers fight back in a similar way, Ryan said ARIN would not back down from the challenge.
“If we find a scheme or artifice to defraud and it’s a substantial number of addresses and its egregious fraud, then yes, we have a reserve set aside for litigation and we can and will use it for cases like this,” Ryan said, adding that he’d welcome anyone with evidence of similar schemes to come forward. “But a better strategy is not to issue it and never have to go back and revoke it, and we’re good at that now.”
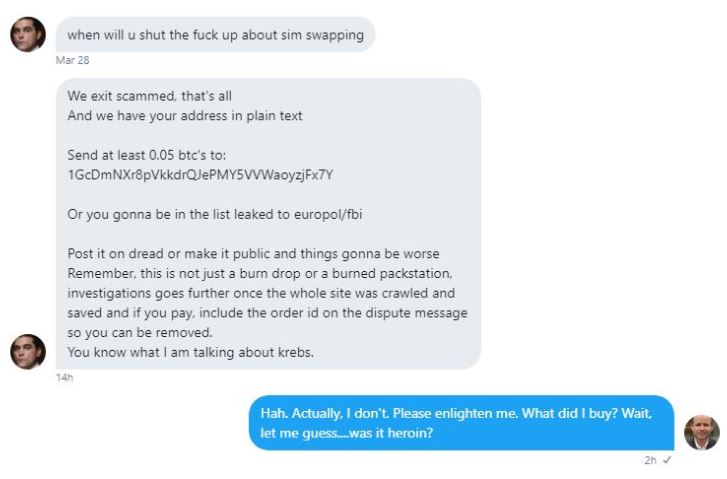
from Krebs on Security http://bit.ly/2YyxLLl
via IFTTT