WiFiMouse 1.8.3.4 – Remote Code Execution (RCE)
from Exploit-DB.com RSS Feed https://ift.tt/yDt2zse
via IFTTT

WiFiMouse 1.8.3.4 – Remote Code Execution (RCE)
from Exploit-DB.com RSS Feed https://ift.tt/yDt2zse
via IFTTT
Wifi HD Wireless Disk Drive 11 – Local File Inclusion
from Exploit-DB.com RSS Feed https://ift.tt/VfTDdju
via IFTTT
A 36-year-old Russian man recently identified by KrebsOnSecurity as the likely proprietor of the massive RSOCKS botnet has been arrested in Bulgaria at the request of U.S. authorities. At a court hearing in Bulgaria this month, the accused hacker requested and was granted extradition to the United States, reportedly telling the judge, “America is looking for me because I have enormous information and they need it.”

A copy of the passport for Denis Kloster, as posted to his Vkontakte page in 2019.
On June 22, KrebsOnSecurity published Meet the Administrators of the RSOCKS Proxy Botnet, which identified Denis Kloster, a.k.a. Denis Emelyantsev, as the apparent owner of RSOCKS, a collection of millions of hacked devices that were sold as “proxies” to cybercriminals looking for ways to route their malicious traffic through someone else’s computer.
A native of Omsk, Russia, Kloster came into focus after KrebsOnSecurity followed clues from the RSOCKS botnet master’s identity on the cybercrime forums to Kloster’s personal blog, which featured musings on the challenges of running a company that sells “security and anonymity services to customers around the world.” Kloster’s blog even included a group photo of RSOCKS employees.
“Thanks to you, we are now developing in the field of information security and anonymity!,” Kloster’s blog enthused. “We make products that are used by thousands of people around the world, and this is very cool! And this is just the beginning!!! We don’t just work together and we’re not just friends, we’re Family.”
The Bulgarian news outlet 24Chasa.bg reports that Kloster was arrested in June at a co-working space in the southwestern ski resort town of Bansko, and that the accused asked to be handed over to the American authorities.
“I have hired a lawyer there and I want you to send me as quickly as possible to clear these baseless charges,” Kloster reportedly told the Bulgarian court this week. “I am not a criminal and I will prove it in an American court.”
Launched in 2013, RSOCKS was shut down in June 2022 as part of an international investigation into the cybercrime service. The Justice Department’s June 2022 statement about that takedown cited a search warrant from the U.S. Attorney’s Office for the Southern District of California, which also was named by Bulgarian news outlets this month as the source of Kloster’s arrest warrant.
When asked about the existence of an arrest warrant or criminal charges against Kloster, a spokesperson for the Southern District said, “no comment.”

The employees who kept things running for RSOCKS, circa 2016. Notice that nobody seems to be wearing shoes.
24Chasa said the defendant’s surname is Emelyantsev and that he only recently adopted the last name Kloster, which is his mother’s maiden name.
As KrebsOnSecurity reported in June, Kloster also appears to be a major player in the Russian email spam industry. In several private exchanges cybercrime forums, the RSOCKS administrator claimed ownership of the RUSdot spam forum. RUSdot is the successor forum to Spamdot, a far more secretive and restricted forum where most of the world’s top spammers, virus writers and cybercriminals collaborated for years before the community’s implosion in 2010.
Email spam — and in particular malicious email sent via compromised computers — is still one of the biggest sources of malware infections that lead to data breaches and ransomware attacks. So it stands to reason that as administrator of Russia’s most well-known forum for spammers, the defendant in this case probably knows quite a bit about other top players in the botnet spam and malware community.
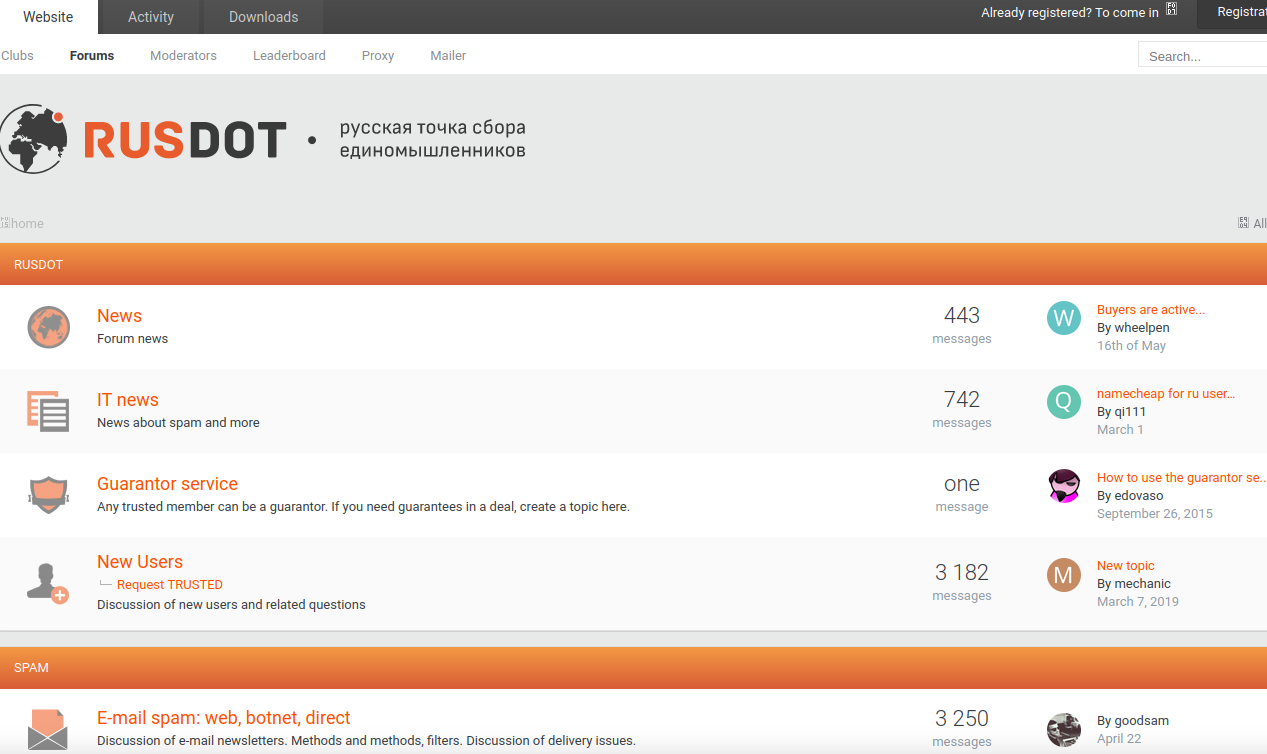
A Google-translated version of the Rusdot spam forum.
Despite maintaining his innocence, Kloster reportedly told the Bulgarian judge that he could be useful to American investigators.
“America is looking for me because I have enormous information and they need it,” Kloster told the court, according to 24Chasa. “That’s why they want me.”
The Bulgarian court agreed, and granted his extradition. Kloster’s fiancee also attended the extradition hearing, and reportedly wept in the hall outside the entire time.
Kloster turned 36 while awaiting his extradition hearing, and may soon be facing charges that carry punishments of up to 20 years in prison.
from Krebs on Security https://ift.tt/a8gzWZR
via IFTTT
CISA says the flaw poses “significant risk” to federal government, adding the Zoho ManageEngine RCE vulnerability to its Known Exploited Vulnerabilities Catalog.
from Dark Reading https://ift.tt/TRBL5PI
via IFTTT
Cybercriminals took control of enterprise Exchange Servers to spread large amounts of spam aimed at signing people up for bogus subscriptions.
from Dark Reading https://ift.tt/4EVlzwX
via IFTTT
Manufacturers need to document a medical device’s intended use and operational environment, as well as plan for misuse, such as a cyberattack.
from Dark Reading https://ift.tt/0aHjoOt
via IFTTT
Critical data on old disks always seems inaccessible if you really need it. But when you DON”T want it back, guess what happens…
from Naked Security https://ift.tt/NwDBiUO
via IFTTT
From creating a software bill of materials for applications your company uses to supporting open source projects and maintainers, businesses need to step up their efforts to help reduce risks.
from Dark Reading https://ift.tt/hMANwoB
via IFTTT
With the update, Microsoft adds features to allow easier deployment of zero-trust capabilities. Considering the 1.3 billion global Windows users, the support could make a difference.
from Dark Reading https://ift.tt/g0oWaw9
via IFTTT
Protecting against risk is a shared responsibility that only gets more complex as you mix the different approaches of common cloud services.
from Dark Reading https://ift.tt/tPwWGKo
via IFTTT