Book Store Management System 1.0.0 – Stored Cross-Site Scripting (XSS)
from Exploit-DB.com RSS Feed https://ift.tt/hAFyJnw
via IFTTT

Book Store Management System 1.0.0 – Stored Cross-Site Scripting (XSS)
from Exploit-DB.com RSS Feed https://ift.tt/hAFyJnw
via IFTTT
WP All Import v3.6.7 – Remote Code Execution (RCE) (Authenticated)
from Exploit-DB.com RSS Feed https://ift.tt/s9QcXiS
via IFTTT
How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW content and privacy threats
The post Staying safe on OnlyFans: The naked truth appeared first on WeLiveSecurity
from WeLiveSecurity https://ift.tt/Cs8eKQO
via IFTTT
How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW content and privacy threats
The post Staying safe on OnlyFans: The naked truth appeared first on WeLiveSecurity
from WeLiveSecurity https://ift.tt/Cs8eKQO
via IFTTT
How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW content and privacy threats
The post Staying safe on OnlyFans: The naked truth appeared first on WeLiveSecurity
from WeLiveSecurity https://ift.tt/Cs8eKQO
via IFTTT
The United Kingdom’s National Crime Agency (NCA) has been busy setting up phony DDoS-for-hire websites that seek to collect information on users, remind them that launching DDoS attacks is illegal, and generally increase the level of paranoia for people looking to hire such services.
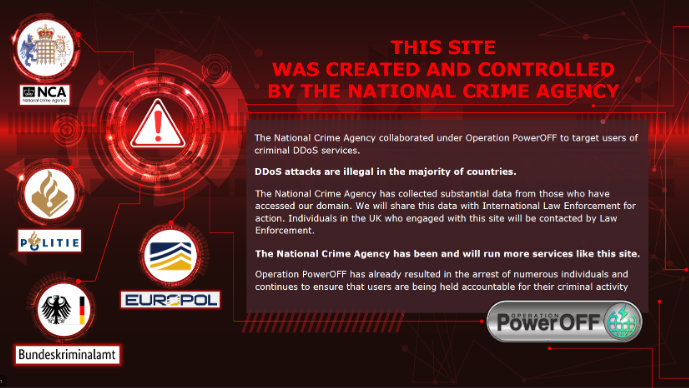
The warning displayed to users on one of the NCA’s fake booter sites. Image: NCA.
The NCA says all of its fake so-called “booter” or “stresser” sites — which have so far been accessed by several thousand people — have been created to look like they offer the tools and services that enable cyber criminals to execute these attacks.
“However, after users register, rather than being given access to cyber crime tools, their data is collated by investigators,” reads an NCA advisory on the program. “Users based in the UK will be contacted by the National Crime Agency or police and warned about engaging in cyber crime. Information relating to those based overseas is being passed to international law enforcement.”
The NCA declined to say how many phony booter sites it had set up, or for how long they have been running. The NCA says hiring or launching attacks designed to knock websites or users offline is punishable in the UK under the Computer Misuse Act 1990.
“Going forward, people who wish to use these services can’t be sure who is actually behind them, so why take the risk?” the NCA announcement continues.
The NCA campaign comes closely on the heels of an international law enforcement takedown involving four-dozen websites that made powerful DDoS attacks a point-and-click operation.
In mid-December 2022, the U.S. Department of Justice (DOJ) announced “Operation Power Off,” which seized four-dozen booter business domains responsible for more than 30 million DDoS attacks, and charged six U.S. men with computer crimes related to their alleged ownership of popular DDoS-for-hire services. In connection with that operation, the NCA also arrested an 18-year-old man suspected of running one of the sites.
According to U.S. federal prosecutors, the use of booter and stresser services to conduct attacks is punishable under both wire fraud laws and the Computer Fraud and Abuse Act (18 U.S.C. § 1030), and may result in arrest and prosecution, the seizure of computers or other electronics, as well as prison sentences and a penalty or fine.
The United Kingdom, which has been battling its fair share of domestic booter bosses, started running online ads in 2020 aimed at young people who search the Web for booter services.
As part of last year’s mass booter site takedown, the FBI and the Netherlands Police joined the NCA in announcing they are running targeted placement ads to steer those searching for booter services toward a website detailing the potential legal risks of hiring an online attack.
from Krebs on Security https://ift.tt/C4oTdrg
via IFTTT
Thinking of trying a bit of DDoSsing to get a feel for life at the fringes of the Dark Side? Don’t do it!
from Naked Security https://ift.tt/sM76DhA
via IFTTT
rukovoditel 3.2.1 – Cross-Site Scripting (XSS)
from Exploit-DB.com RSS Feed https://ift.tt/Svok4hA
via IFTTT
Senayan Library Management System v9.5.0 – SQL Injection
from Exploit-DB.com RSS Feed https://ift.tt/NPKm2Qx
via IFTTT
iBooking v1.0.8 – Arbitrary File Upload
from Exploit-DB.com RSS Feed https://ift.tt/nBXkoRv
via IFTTT